

Archived Insight | December 9, 2021
Recognizing that cybersecurity is an increasingly critical issue, sponsors of ERISA retirement plans are taking steps to reduce risks. Those efforts should now account for the fact that when the DOL reviews what plans are doing, it is looking to the guidance on cybersecurity best practices and security tips that it released in April 2021.
That DOL guidance aimed at reducing cybersecurity risks in ERISA plans is the first official guidance from the DOL on this increasingly critical issue. We summarized the DOL guidance in our April 21, 2021 insight.

Share this page
Plan sponsors may wish to review their own current cybersecurity practices, including reviewing their service-provider contracts, as well as initiating ongoing surveying of those same vendors, to ensure they are acting in accord with the practices that the DOL has identified.
Plan sponsors should consider this new guidance as they select and monitor the plan service providers that have access to sensitive, confidential plan-related data and information. This data includes personally identifiable information (PII), electronic protected health information (ePHI), or sensitive trust information (e.g., surrounding banking).
Plans should review their vendors’ practices to assure that trustees are meeting these new fiduciary best practices. Trustees may find it necessary to retain a cybersecurity expert who is also knowledgeable about ERISA trusts and plans to audit vendors’ practices.
Finally, plan sponsors should review existing insurance policies and determine whether cybersecurity insurance changes would be appropriate.
Below are three steps plan sponsors should consider taking to ensure their cybersecurity efforts are aligned with the DOL’s recommendations.
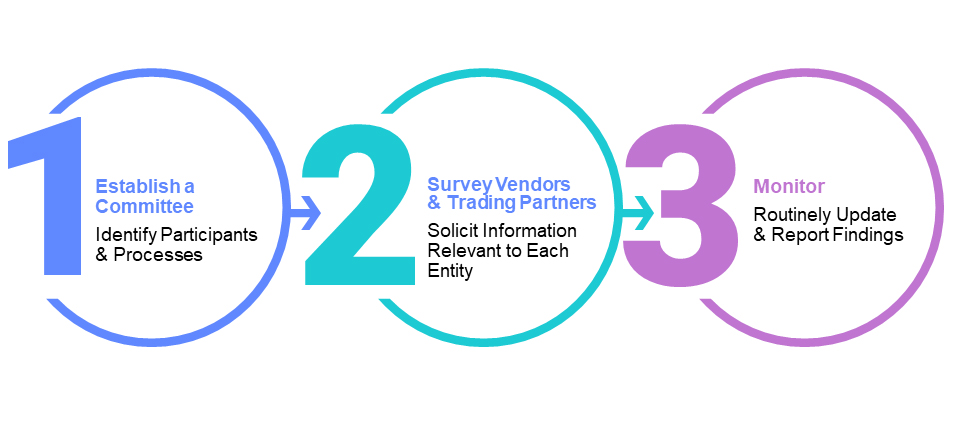
The first suggestion is to create a formal or informal information security governance committee. This committee will help ensure clarity and consistency in practices within the areas of responsibility for cybersecurity among the plan’s administrative function (i.e., the fund office or third-party administrator), non-administrative third parties, vendors and trading partners who all access and store sensitive or confidential plan-related data and information.
If formally empaneled as part of the board of trustees, the committee could be a subset of plan trustees and legal counsel (often with input from other professionals knowledgeable in both cybersecurity and ERISA trust administration and operations). An informal committee may be more typically comprised of the plan administrator, legal counsel and other professionals.
One of the most common mistakes organizations make is that they build their committees and then launch into their first meeting without any type of charter (defining the general responsibilities of the committee). Without defined inputs and outputs, a committee does not have the information it needs to execute effectively on its responsibilities and, consequently, is unable to meet its stated goals.
An information security governance committee’s core responsibility should be to provide strategic cybersecurity governance and oversight of the fund office or TPA that administers the plan, as well as the multiple and varied vendors, third parties and recordkeepers that are performing services on behalf of the plan.
Some high-level areas the committee should focus on include:
The committee should consider the potential for external and internal threats and threats arising from transactions with their own trusted third parties and other vendors (e.g., vendors that serve the plan’s vendors.) The committee should also review privacy and information security policies and standards and the ramifications of any updates to policies and standards. The committee will need to define which vendors it will survey and what metrics it will monitor, and how often this will occur (it should not be a “one-and-done” exercise; it should be viewed as an ongoing commitment of the plan).
In keeping with the spirit of the DOL guidance regarding plan sponsors’ fiduciary responsibilities, plan sponsors should survey their key vendors to ensure they are acting in accord with the best practices the DOL has identified. Potential vendors to survey and monitor can include recordkeepers of PII, ePHI and/or other sensitive and confidential data and information related to the plan (e.g., financial information).
What are the committee’s purposes and responsibilities? These can include governing the use of health, pension and financial data, by third parties, recordkeepers and vendors. For each domain, identify which vendors and associated metrics to survey and monitor. This will help determine the relative importance of the vendors to participants or all stakeholders.
Ranking vendors’ potential risk to the organization will help determine how often to survey them on an ongoing basis.
Sample topic areas about which to survey vendors, include, but are not limited to:
The committee should assess vendors’ survey responses for how complete and current they are and consider how well they align with industry standards and how well they are communicated.
There are many possible ongoing metrics to monitor. The following chart lists just a few of the many potential high-level data and information categories the committee could include in its vendor monitoring.
| Category | What to Look For |
| Internet or external security audit reports | Outstanding findings or omissions |
| Recent internal or external security risk assessments | Any outstanding findings |
| Security compliance obligations and reports | Compliance risks, including HIPAA assessments, SSAE 18 |
If the committee recommends replacing a vendor, it can refer to the DOL’s tips for hiring one that has strong cybersecurity practices.

Insurance, Technology, Cybersecurity Awareness Month, Cybersecurity consulting

Insurance, Cybersecurity consulting, Multiemployer Plans, Public Sector, Healthcare Industry, Higher Education, Architecture Engineering & Construction, ATC, Cyber Advisor, Cybersecurity Awareness Month, Risk Mitigation

Retirement, Technology, Cybersecurity consulting, Risk Mitigation
This page is for informational purposes only and does not constitute legal, tax or investment advice. You are encouraged to discuss the issues raised here with your legal, tax and other advisors before determining how the issues apply to your specific situations.
Don't miss out. Join 16,000 others who already get the latest insights from Segal.
© 2026 by The Segal Group, Inc.Terms & Conditions Privacy Policy Style Guide California Residents Sitemap Disclosure of Compensation Required Notices